Understanding the Different Types of DDoS Attacks

Table of Contents
As the internet becomes more integral to everyday business operations, cybersecurity threats evolve in both complexity and impact. One of the most persistent and damaging threats facing organizations today is the Distributed Denial of Service (DDoS) attack. These attacks flood a targeted system with an overwhelming amount of traffic, rendering services unusable for legitimate users.
To effectively mitigate DDoS threats, it’s essential to understand the various types of attacks cybercriminals deploy. Each type targets a specific layer of the network or system infrastructure, and knowing how each one operates is the first step toward building a resilient defense strategy.
In this post, we’ll explore the main types of DDoS attacks, breaking them down into their categories and detailing how they disrupt services.
1. Volume-Based Attacks
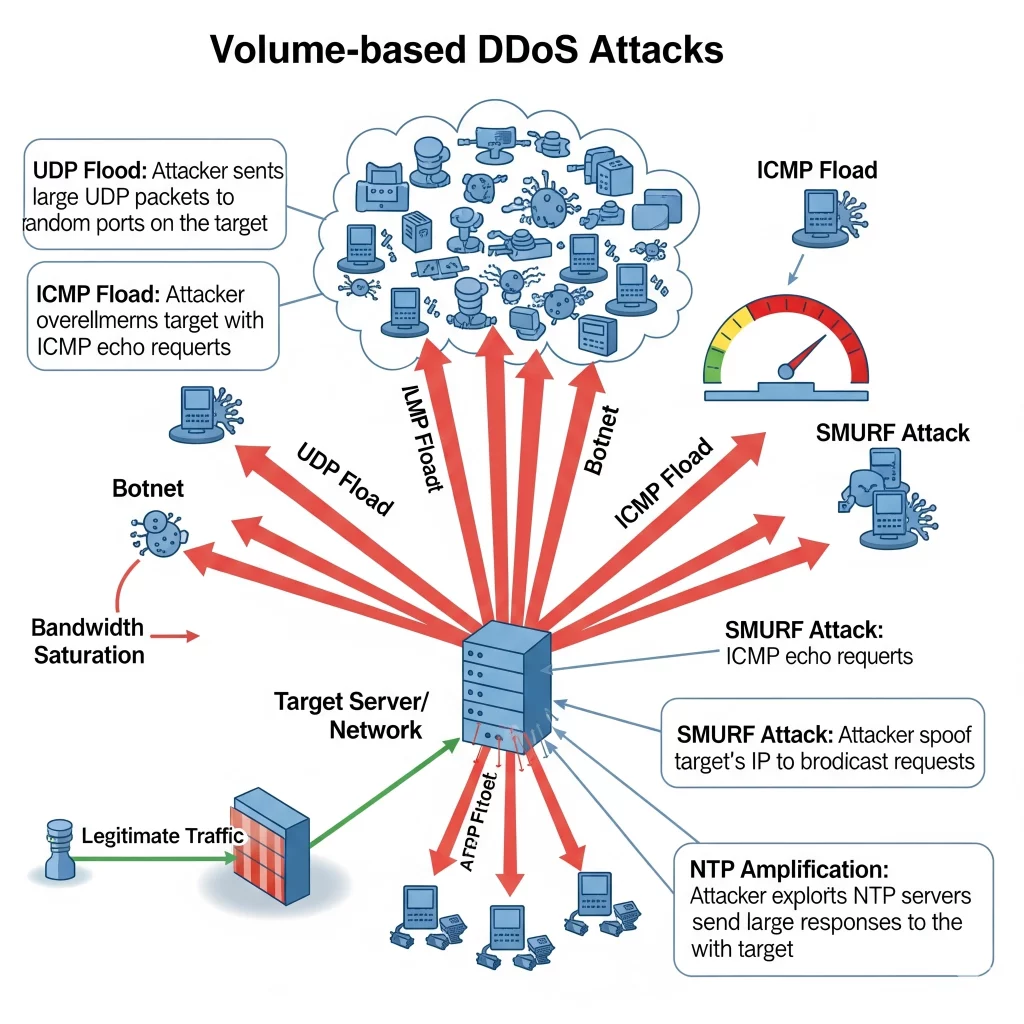
Volume-based DDoS attacks aim to saturate the bandwidth of the target site. They are the most common type and often involve botnets sending massive amounts of traffic.
Key Examples:
- UDP Flood: A large number of UDP packets are sent to random ports on the target machine, forcing it to respond continuously.
- ICMP Flood: This uses ICMP echo requests (pings) to flood the target, consuming both outgoing and incoming bandwidth.
- DNS Amplification: Attackers spoof the victim’s IP and send DNS queries to open DNS resolvers, which respond with large amounts of data, amplifying the traffic hitting the target.
Impact:
These attacks are designed to consume all available bandwidth, effectively taking the target offline by exhausting its capacity.
2. Protocol Attacks
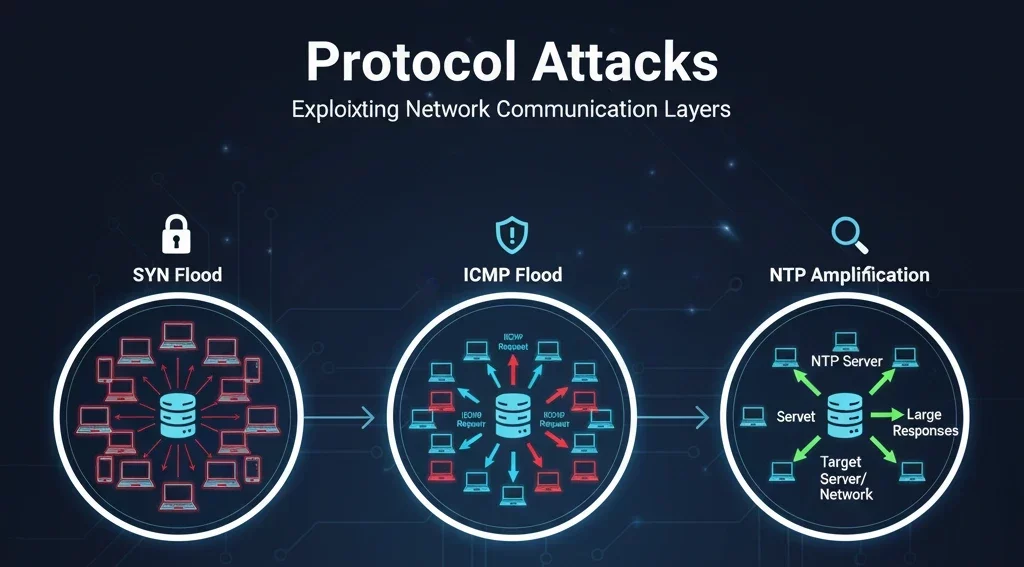
Protocol attacks exploit weaknesses in network layer protocols. These attacks target servers and intermediate resources like firewalls and load balancers.
Key Examples:
- SYN Flood: Exploits the TCP handshake process by sending repeated SYN requests with spoofed IP addresses, never completing the connection.
- Ping of Death: Sends maliciously crafted ping packets that exceed the maximum allowed size, causing systems to crash or reboot.
- Smurf Attack: An attacker sends ICMP requests with a spoofed source address (the victim) to a network’s broadcast address, causing a flood of responses.
Impact:
These attacks consume server resources, and because they target the infrastructure itself, they can be harder to detect and mitigate.
3. Application Layer Attacks
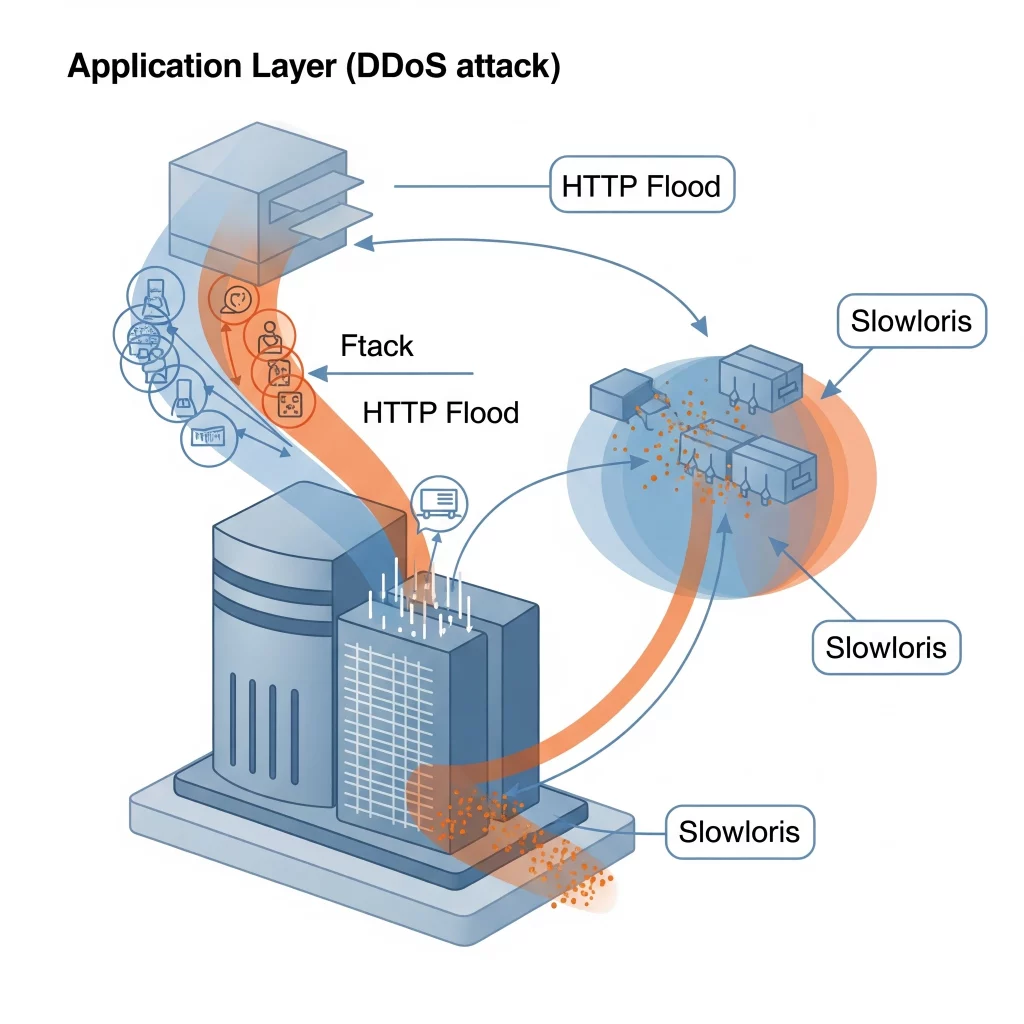
Application layer (Layer 7) attacks mimic legitimate user behavior, making them difficult to distinguish from normal traffic. They target the actual applications, such as web servers.
Key Examples:
- HTTP Flood: Attackers send seemingly legitimate HTTP requests, overwhelming the web server’s capacity to process requests.
- Slowloris: Keeps many connections to the target web server open and holds them open as long as possible by sending partial HTTP requests.
- Zero-day Exploits: These attacks exploit unknown or unpatched vulnerabilities in applications to cause crashes or service interruptions.
Impact:
These attacks are highly stealthy and resource-intensive, aiming to exhaust application resources rather than network bandwidth.
4. Multi-Vector Attacks
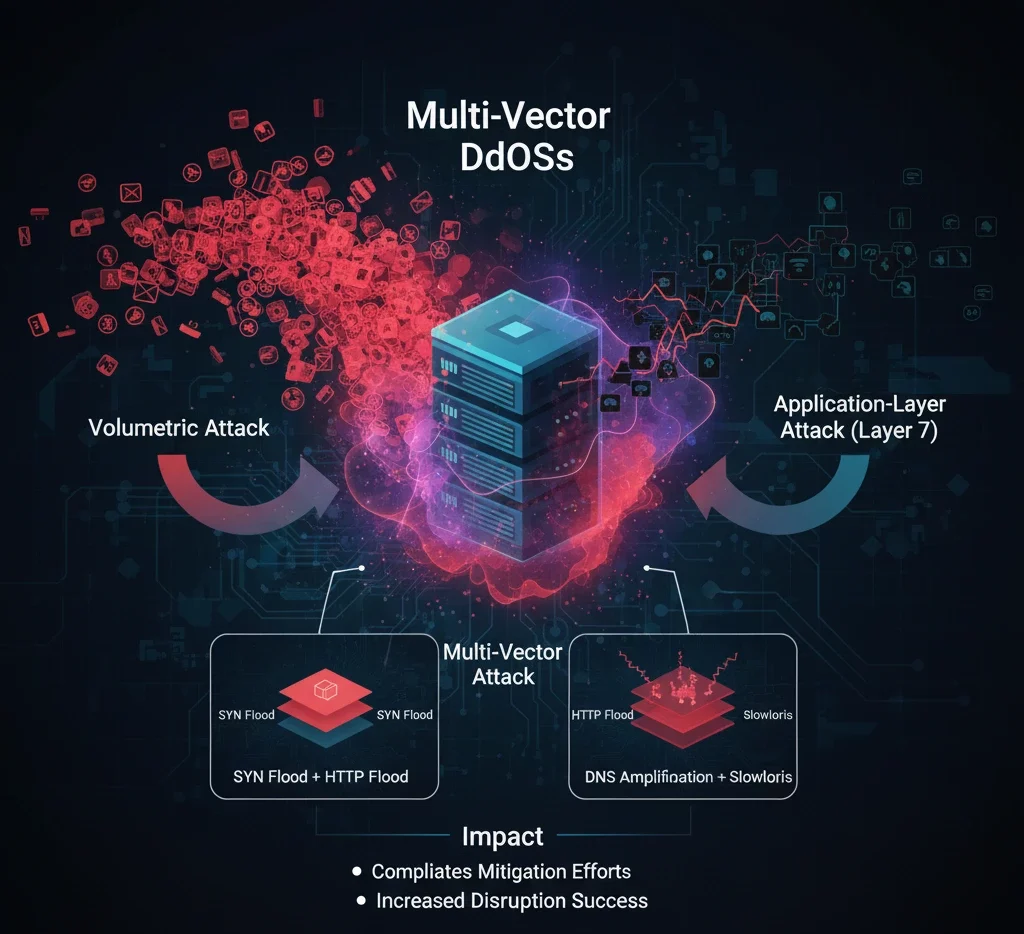
Multi-vector attacks combine two or more different types of DDoS strategies. For example, an attacker might initiate a volumetric attack while simultaneously targeting the application layer.
Key Examples:
- Combining SYN floods with HTTP floods.
- Using DNS amplification in conjunction with Slowloris.
Impact:
By mixing attack types, these methods complicate mitigation efforts and increase the chance of successful disruption.
Why It Matters
Understanding these DDoS variations is critical for implementing a comprehensive defense. Organizations must deploy layered security solutions, conduct regular vulnerability assessments, and ensure that both infrastructure and applications are equipped to detect and mitigate DDoS activity.
In addition to traditional firewalls and intrusion prevention systems, DDoS protection services and real-time traffic monitoring tools play vital roles in identifying and mitigating threats before they escalate.
Final Thoughts
DDoS attacks are becoming more sophisticated, but with a deep understanding of how each type functions, businesses can stay one step ahead. A well-informed security posture, complemented by robust mitigation strategies, is essential for safeguarding your digital presence.
Trusted IPv4 Leasing for Business Growth
Get enterprise-grade IPv4 space quickly, with seamless deployment and end-to-end management.
Get Started with i.leaseRelated Blogs
Related Posts
How much does a /24 IPv4 block cost in 2026?
IPv4 scarcity continues to shape internet infrastructure, with /24 blocks still trading actively on global markets despite growing IPv6 adoption. Key points A /24 IPv4 block usually costs between $6,000 and $15,000 in 2026. Cloud providers, hosting companies and SaaS providers need IPv4 addresses so prices stay high. IPv4 addresses are like an asset because they are scarce. What is a /24 IPv4 block A /24 IPv4 blockRead more Related Posts How much does a /24 IPv4 block cost in 2026? IPv4 scarcity continues to shape internet infrastructure, with /24 blocks still trading actively on global markets despite growing IPv6 adoption. Key Read more The future of IPv4 markets Despite IPv6 expansion, scarcity keeps IPv4 valuable, sustaining a global secondary market where addresses increasingly function as tradable digital assets.Finite Read more Common Myths About Selling IP Addresses The IPv4 secondary market is often shrouded in mystery, leading many organizations to sit on valuable digital assets because they Read more .related-post {} .related-post .post-list { text-align: left; } .related-post .post-list .item { margin: 5px; padding: 10px; } .related-post .headline { font-size: 18px !important; color: #999999 !important; } .related-post .post-list .item .post_thumb { max-height: 220px; margin: 10px 0px; padding: 0px; display: block; } .related-post .post-list .item .post_title { font-size: 16px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } .related-post .post-list .item .post_excerpt { font-size: 13px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } @media only screen and (min-width: 1024px) { .related-post .post-list .item { width: 30%; } } @media only screen and (min-width: 768px) and (max-width: 1023px) { .related-post .post-list .item { width: 90%; } } @media only screen and (min-width: 0px) and (max-width: 767px) { .related-post .post-list .item { width: 90%; } }

The future of IPv4 markets
Despite IPv6 expansion, scarcity keeps IPv4 valuable, sustaining a global secondary market where addresses increasingly function as tradable digital assets. Finite IPv4 supply has created a mature secondary market where address blocks are bought, sold and leased worldwide. Prices fluctuate, but persistent demand from cloud, hosting and AI infrastructure suggests IPv4 markets will remain active for years. What happened The rise of a digital commodity The global market forRead more Related Posts How much does a /24 IPv4 block cost in 2026? IPv4 scarcity continues to shape internet infrastructure, with /24 blocks still trading actively on global markets despite growing IPv6 adoption. Key Read more The future of IPv4 markets Despite IPv6 expansion, scarcity keeps IPv4 valuable, sustaining a global secondary market where addresses increasingly function as tradable digital assets.Finite Read more Common Myths About Selling IP Addresses The IPv4 secondary market is often shrouded in mystery, leading many organizations to sit on valuable digital assets because they Read more .related-post {} .related-post .post-list { text-align: left; } .related-post .post-list .item { margin: 5px; padding: 10px; } .related-post .headline { font-size: 18px !important; color: #999999 !important; } .related-post .post-list .item .post_thumb { max-height: 220px; margin: 10px 0px; padding: 0px; display: block; } .related-post .post-list .item .post_title { font-size: 16px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } .related-post .post-list .item .post_excerpt { font-size: 13px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } @media only screen and (min-width: 1024px) { .related-post .post-list .item { width: 30%; } } @media only screen and (min-width: 768px) and (max-width: 1023px) { .related-post .post-list .item { width: 90%; } } @media only screen and (min-width: 0px) and (max-width: 767px) { .related-post .post-list .item { width: 90%; } }
Inbound vs. Outbound IPv4 Leasing: A Complete Guide for Enterprises
Understanding IPv4 leasing helps enterprises manage scarce address space, reducing risk and unlocking strategic growth opportunities in today’s digital economy. Key points Distinguishes between inbound (leasing in) and outbound (leasing out) IPv4 approaches and their strategic implications. Highlights contract structures, registry risk management and continuity considerations affecting global number resources. Inbound vs. outbound IPv4 leasing: complete enterprise guide In the post-exhaustion era of Internet Protocol version 4 (IPv4),Read more Related Posts How much does a /24 IPv4 block cost in 2026? IPv4 scarcity continues to shape internet infrastructure, with /24 blocks still trading actively on global markets despite growing IPv6 adoption. Key Read more The future of IPv4 markets Despite IPv6 expansion, scarcity keeps IPv4 valuable, sustaining a global secondary market where addresses increasingly function as tradable digital assets.Finite Read more Common Myths About Selling IP Addresses The IPv4 secondary market is often shrouded in mystery, leading many organizations to sit on valuable digital assets because they Read more .related-post {} .related-post .post-list { text-align: left; } .related-post .post-list .item { margin: 5px; padding: 10px; } .related-post .headline { font-size: 18px !important; color: #999999 !important; } .related-post .post-list .item .post_thumb { max-height: 220px; margin: 10px 0px; padding: 0px; display: block; } .related-post .post-list .item .post_title { font-size: 16px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } .related-post .post-list .item .post_excerpt { font-size: 13px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } @media only screen and (min-width: 1024px) { .related-post .post-list .item { width: 30%; } } @media only screen and (min-width: 768px) and (max-width: 1023px) { .related-post .post-list .item { width: 90%; } } @media only screen and (min-width: 0px) and (max-width: 767px) { .related-post .post-list .item { width: 90%; } }